What to Expect in NIST SP 800-53 Revision 5
- Written by: Jeff Hudgens
If your organization uses the National Institute of Standards and Technology’s (NIST) Special Publication (SP) 800-53 Revision 4, Security and Privacy Controls for Federal Information Systems and Organizations, you are probably already aware that efforts are underway to develop Revision 5. NIST, as always, has solicited and received a substantial number of comments regarding the current document, as well as recommendations for adjusting the document to better suit non-federal entities, including businesses, academia, and state, local and tribal governments. As more and more non-federal entities adopt and use NIST standards, NIST is taking steps to make the controls catalogue more adaptable and usable for a broad array of organizations.
The following information summarizes the expected changes:
- To be more inclusive, the term “federal” will be removed to the extent possible.
- The term “information system” will be replaced with just “system” to be more inclusive of various types of systems, such as industrial control systems and Internet of Things.
- To improve the documents structure, and to make it easier to find and compare controls, both the program management and privacy controls sections will be integrated into the main controls section. This change enhances the relationship between privacy and security controls, and reinforces the importance of overall program management of information security activities within organizations.
- Priority sequencing codes (i.e., P0, P1, P2, P3) will be removed. Feedback indicated that the intent for these codes was being misinterpreted; however, removing them provides organizations with better flexibility in sequencing the implementation of controls.
- Keywords and hyperlinks will be integrated to assist users in navigating the document and finding information.
- Introductory terms within the controls (i.e., “The organization…” and “The information System…”) will be removed to make the controls “outcome-based,” to better align the controls with other NIST guidance, and to remove ambiguity regarding responsibility for implementing the controls.
NIST is planning on releasing the first draft of Revision 5 for public comment at the end of March 2017. If you are interested in additional information from NIST about the expected changes, please visit: http://csrc.nist.gov/publications/drafts/800-53r5/draft_sp800-53-rev5_update-message.pdf
For a copy of the current SP 800-53 Revision 4, as well as other NIST SP 800 series documents, please visit: http://csrc.nist.gov/publications/PubsSPs.html
Related Content
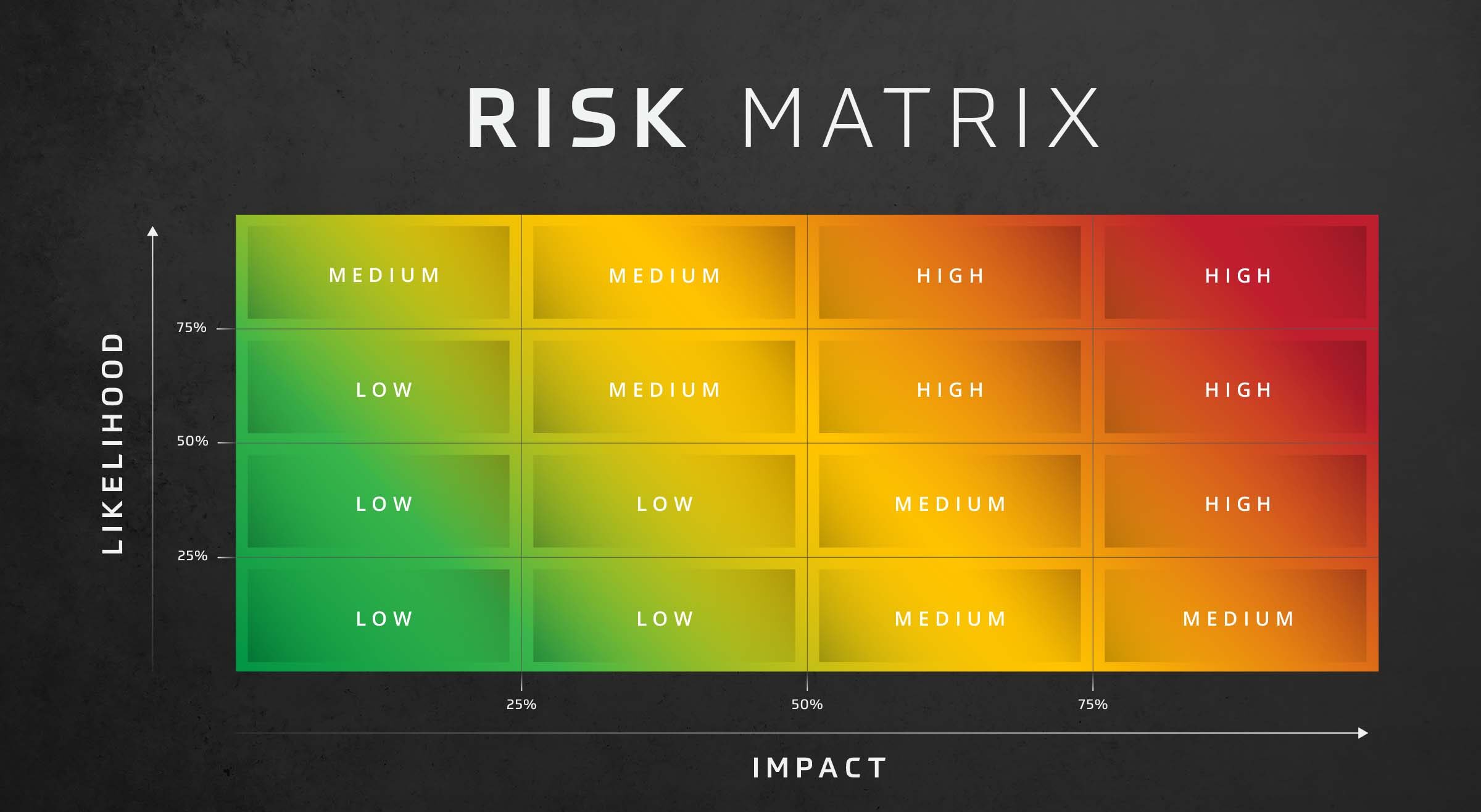
Risk Assessment: Likelihood and Impact
Assess risk effectively with the risk assessment likelihood and impact matrix. This decision-making matrix assesses risk based on the likelihood and impact of threats in your organization.

Cybersecurity Risk Assessment
Optimize your security with an HBS Cybersecurity Risk Assessment. Identify vulnerabilities, manage risks, improve your cybersecurity posture.

IT Company Assessing Risk to Protect Clients
A company managing clients’ IT infrastructure can’t afford a breach. That’s why this IT solution provider took recommendations from their colleagues and hired HBS to conduct a risk assessment.