Why Do I Need an IT Risk Assessment?
- Written by: Megan Soat

Some organizations are required by law to conduct a risk assessment; others are bound by compliance or pressured by clients. Even when it isn’t mandatory, many organizations choose to perform a risk assessment for the various benefits it provides. In this article we will talk about why they do perform, and the reasons every organization should consider, a risk assessment.
For starters, an IT risk assessment is a great way to gain a better understanding of an organization’s technology environment. An assessment helps in guiding the establishment of a security plan and creating a roadmap for achieving security goals. If you have been tasked as the information security lead, this is where you should begin.
Conducting an IT risk assessment is a proactive approach to securing your organization. Well-organized assessments utilize a structured framework that helps identify existing controls as well as gaps that have gone unnoticed. Without an assessment, these findings would be left hidden and unaddressed.
The results of the assessment, however, are only the beginning. What an organization does with those results is where they find the value. By evaluating the comprehensive list of risks an organization can determine the biggest threats, prioritize them, and create a plan for mitigation.
It is the IT Directors’ (and others in a similar role) responsibility to identify the risks and present them to the executive team. For it is the execs who are responsible for making the business decision that they believe is best for the organization. IT Directors can provide recommendations and guidance, but the decision to accept, mitigate, or transfer the risk is that of the business and its leaders.
Effectively communicating risks with executives isn’t always an easy task for IT professionals. It is important to arm yourself with results and actionable recommendations prior to communicating concerns. This will help you in your efforts to relay important security information. Providing the management team with a plan that is prioritized and concise may just enable you to get those necessary security resources after all.
It is also important to remember that threats are changing constantly, and a risk assessment is simply the beginning of building an effective IT Risk Management Program. For those of you just dipping your toes into the murky waters of information security, a risk assessment will help you take that leap and dive head first with confidence. Don’t wait until someone else uncovers a vulnerability for you. Be proactive by identifying the risks and allowing it to be the business’ decision on how to deal with them.
Related Content
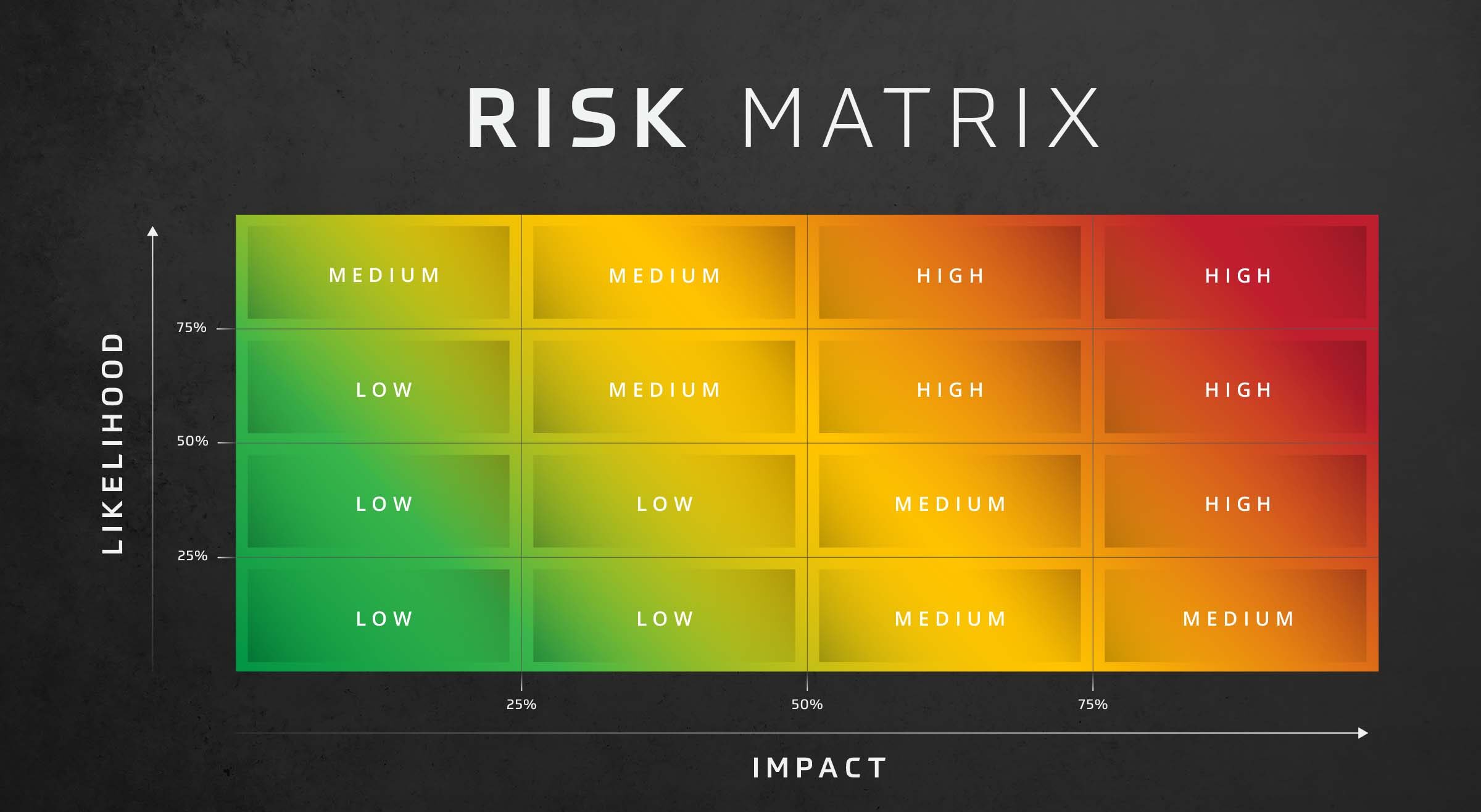
Risk Assessment: Likelihood and Impact
Assess risk effectively with the risk assessment likelihood and impact matrix. This decision-making matrix assesses risk based on the likelihood and impact of threats in your organization.

Cybersecurity Risk Assessment
Optimize your security with an HBS Cybersecurity Risk Assessment. Identify vulnerabilities, manage risks, improve your cybersecurity posture.

IT Company Assessing Risk to Protect Clients
A company managing clients’ IT infrastructure can’t afford a breach. That’s why this IT solution provider took recommendations from their colleagues and hired HBS to conduct a risk assessment.