How Should I Respond to My Clients’ Security Requests?
- Written by: Megan Soat - HBS Director of Cybersecurity

Vendors are often asked by clients to supply some sort of proof they will protect the client’s sensitive data. While this may seem like a reasonable request, knowing how much information to share and the best way to do that is important.
As a vendor, you may receive multiple requests from clients for compliance reports or third party validated security reports, such as a SOC 2. If you don’t have a third-party validated report, the client may ask you to complete a security questionnaire. (Something we discussed in a recent blog, here.) That process can be very time consuming, especially with multiple questionnaires asking for different information.
We’ve created five guidelines to help vendors meet their clients’ needs, without risking their own security:
1. Analyze your relationship with the client.
Sometimes clients will send out questionnaires to every vendor they use, without really looking at what that vendor has access to. If you are a vendor, but do not deal with the client’s sensitive data or systems, you may not need to fill out tedious questionnaires. That client could be following their own company protocol without considering each request being made.
2. Know which data you should provide your client.
We typically don’t advise vendors to share Policies, Standards, and Procedures with a client. This sort of information could put you, the vendor, at risk. Be cautious and make sure you’re not sharing more information than what is required and the information you’re sharing doesn’t risk your own companies’ security to comply with a client’s wishes. It is always recommended to have the client execute a non-disclosure agreement (NDA) prior to sending over any information and reports.
3. Know when to push back, and how.
If a client asks for more information than you’re comfortable with, you have the right to object. Oftentimes this will be a conversation, rather than a finite “no." Ask for your client’s reasoning for the information they’re requesting. If it is still too much, explain why you are uncomfortable with the situation.
4. Offer up an alternative.
If you’ve turned down the client’s questionnaire or request for your Policies, Standards, and Procedures, they may still need some proof that you are ready to protect their security interests.
- One way to do that is with a pre-filled questionnaire or overview doc of your security controls. One widely recognized questionnaire is the. SIG (Standardized Information Gathering). This questionnaire allows vendors to create a standard form response, ready to be handed out, which can save your organization significant time. You can also create an overview document which may include at a high-level security controls you have in place, inventory of your Policies and Standards with only the Table of Contents visible, etc. This shows that controls are in place but doesn’t give all the details.
- Another option is to set up a meeting with the client. This can be a video call with screen sharing, or a webinar. If you plan to show the client any sensitive data, make sure they do not screen-grab or record the conversation.
- If a client requests a SOC 2 report, but you have another form of compliance report already completed, ask the client if that will work instead. They may be able to accept a different type of third party validated report, even if they did not specifically ask for it.
5. Decide if this client is worth the effort.
Completing compliance reports, filling out dozens of questionnaires, and sharing sensitive data can come at a cost to you. You need to decide if the client in question is worth the time and resources their requests will take. Sometimes it’s more cost-effective to let that client go than to jump through more hoops.
Hopefully this helps you know how to handle the inevitable security requests vendors face! If you need more assistance with responding to client requests or knowing which information may be too sensitive to share, be sure to reach out to a cybersecurity expert.
Related Content
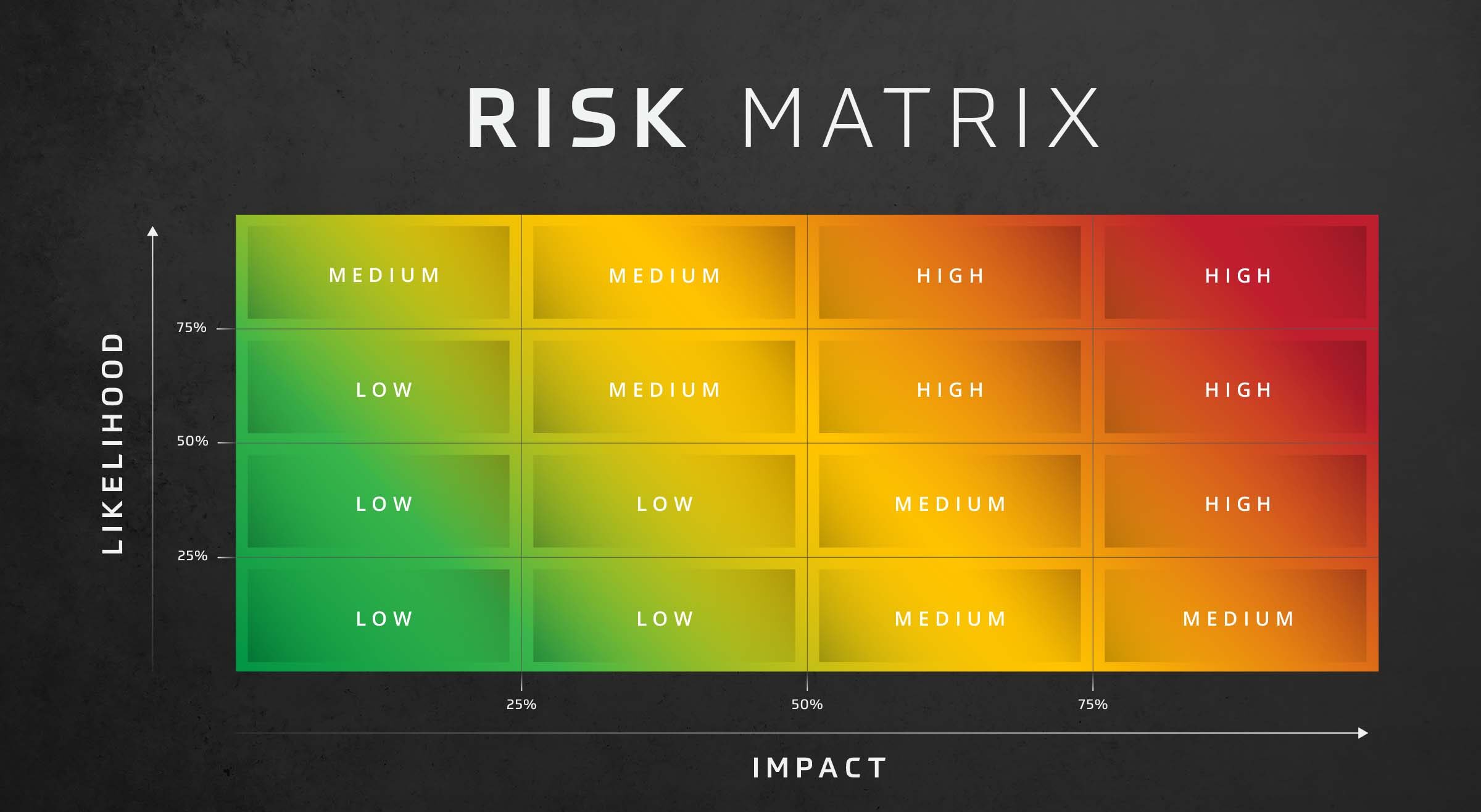
Risk Assessment: Likelihood and Impact
Assess risk effectively with the risk assessment likelihood and impact matrix. This decision-making matrix assesses risk based on the likelihood and impact of threats in your organization.

Best Practices for Third-Party Risk Management
Learn how to protect your business with third party risk management (TPRM). Best practices, vendor assessments and frameworks explained.

Analyzing and Assessing Third-Party Security Reports
Assessing and analyzing third-party vendors should be a top priority. Here are a few things to consider while reviewing a vendor’s security program.