Analyzing and Assessing Third-Party Security Reports
- Written by: Matthew McGill and Sammi LaBello

Working with vendors is necessary for many businesses, no matter the size. That often means giving sensitive data to people outside the comfort of your own company walls. While the extra help can be crucial to the growth of your organization, it can also open yourself and clients to possible risk. A mature vendor management program is paramount for the protection of your data.
So where do you start?
First, you need to identify your critical vendors. You should be devoting extra attention to these vendors because they could be the highest risk to your organization.
How do you know if vendors are protecting your data?
One way to double-check the safety of your information is to look over your vendors’ third party validated reports. These reports are conducted by an outside auditor to review the security programs a vendor has in place.
Compliance reports will reveal the scope, gaps, exceptions, and complementary user entity controls.
- Scope shows what the report covers. This is where the auditor lays out exactly what is being reviewed in the vendor’s security. This helps a business reading the report know how the results correlate with the way they will work with the vendor.
- Gaps and exceptions are the items or practices missing from a vendor’s security program. These can be either minor or major. It may take an IT expert to determine what is worthy of concern, and what may be passable.
- Complementary user entity controls explain what the business is responsible for in the security process. This lays out the procedures a business should have in place to protect itself when working with a vendor.
One example of a third party validated report is a SOC 2 report. While these reports can be a wealth of knowledge for a business, not all organizations will have them available. That means you need to find alternative ways to determine the security practices of your vendors. One way to do so is by asking a lot of questions!
Questionnaires can help when SOC 2 reports are missing.
Questionnaires are a way to evaluate a vendor’s security program. This will include questions about how they plan to protect your data, and what practices are already in place.
There are a few ways you can come up with a valuable questionnaire. They can be written by internal IT staff; just make sure you verify their knowledge of compliance reports. If they don’t feel comfortable creating the questionnaire, another option is outsourcing the job to a cybersecurity firm. Once the questionnaire is sent to the vendor, they should be able to fill out each question with ease. Not being able to do so could raise concerns.
Another red flag would be a vendor who has a SOC 2 report but refuses to share it with the business. Sharing SOC 2 results is a common practice and they should not be withheld from organizations working with that vendor. However, it is acceptable for vendors to request a non-disclosure agreement prior to delivering the report.
Do not settle for knowing a SOC 2 report is there.
Often business owners will ask a vendor if they have a SOC 2 report, but they never actually review the results. Simply having a SOC 2 report done does not mean the vendor is secure. Assess and analyze the results. Then determine if that vendor is going to protect your company’s sensitive data. Your data is one of your most precious assets. Don’t leave it to chance in the hands of unsecure vendors.
If you receive compliance reports, but still have no idea what they mean, there are cybersecurity experts ready to help!
Related Content

Why Do You Need a SOC 2® Report?
Do you need to get a SOC 2® report? Discover six reasons why you may need a SOC 2® security report to create a competitive advantage and attract new clients.

Security Requirements of Vendors and Clients
As security awareness rises, so do expectations of vendors and clients. Organizations have begun including information security in their due diligence process.
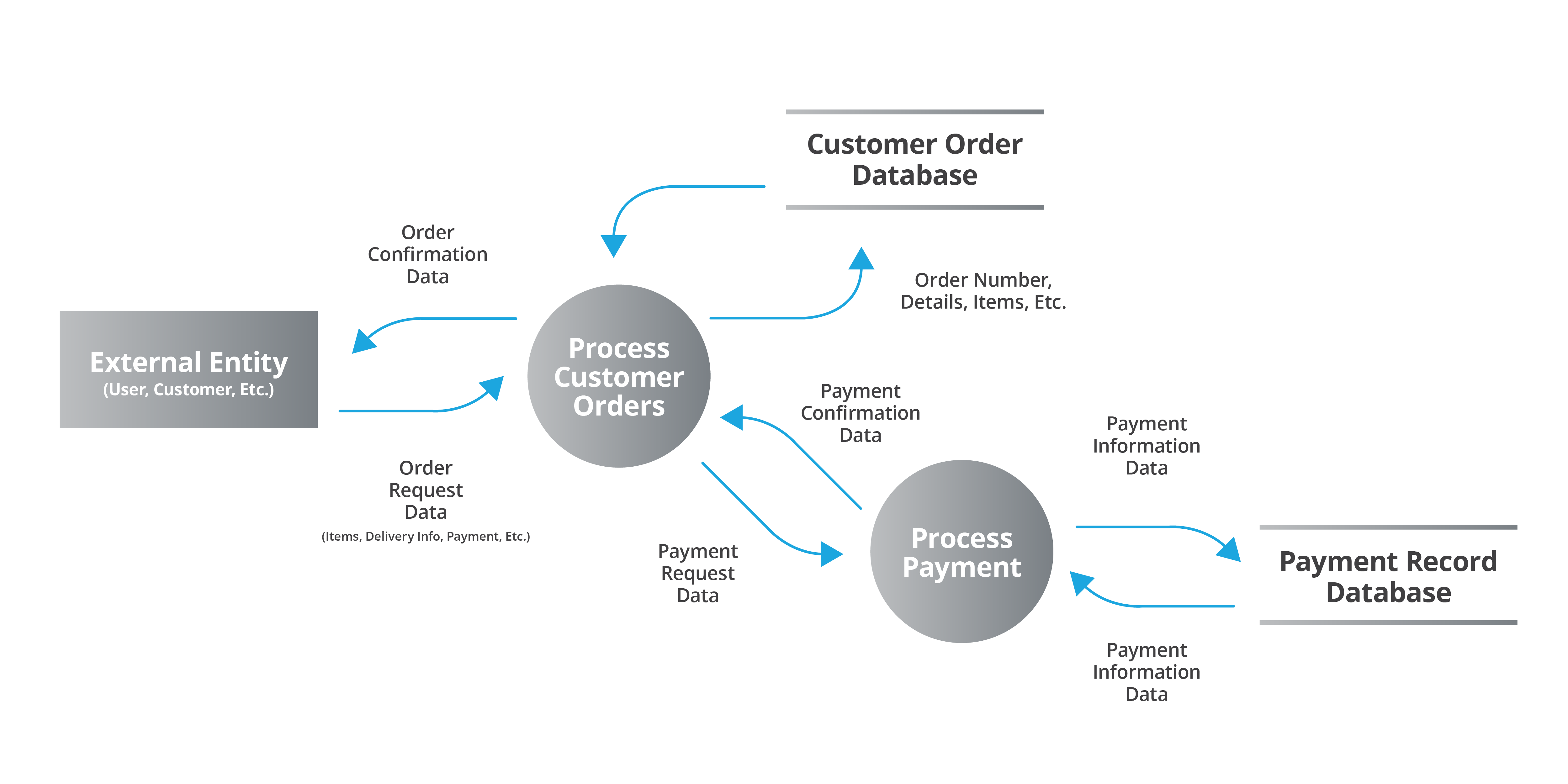
Why You Need a Data Flow Diagram (DFD)—and How to Create One
Data flow diagrams (DFDs) reveal risks, simplify complex systems, and enhance security. We’ll show you step-by-step guidance so you can create your own DFD.