Information Security vs. Information Assurance
- Written by: Dave Nelson
One of the questions commonly asked of me is about the employment outlook for information security professionals. For starters, it’s fantastic. You’ll have no problem getting a job in information security, if you want it. This should not be confused with - You’ll have your pick of the perfect job in the industry you want, at the company of your choosing and with a salary only a king could scoff at. No, it means there are plenty of jobs. You’ll need to put in the time and effort to build the skillset and experience to be hired into your dream job. You just won’t have to tell your parents you’re moving back in because all of the information security positions have been eliminated in the latest round of corporate cuts.
The difference between Information Security and Information Assurance
I then immediately begin thinking about the difference between Information Security (InfoSec) and Information Assurance (IA). Information security is just like any other career field. There are multiple paths you can take within the field, depending on your interest. The skill sets needed to be effective in these two roles can be very different. Now certainly title isn't everything, and one company uses the term security where the other uses assurance. The US government is quite fond of the information assurance moniker. However, within the profession, we are starting to see a marked delineation between Information Security and Information Assurance. This is similar to the split of information security and information privacy.
InfoSec has traditionally been very technology focused. The daily operations of security applications and infrastructure such as firewall, intrusion prevention systems, counter hacking, etc. Penetration testing and vulnerability analysis of systems are other examples. Information Assurance has been more involved with assessing the overall risk of an organization's technology and working to mitigate that risk. While there is certainly a technology component, it's not a pronounced as with InfoSec.
The Need for Standardized Terminology
Perhaps I'm splitting hairs or focusing too much on semantics for some of you, but I see a real need to evaluate the terminology we use as our profession matures. We have seen the abstracting of privacy professionals from the security group. We are now beginning to see specialization within the InfoSec ranks, like we've seen in other technology professions. Some DBA (Database Administrator) professionals specialize in architecture, while others deal only with implementation and performance. I think we are seeing a similar maturity in the Information Security/Privacy/Assurance world. As more work is tossed our way and teams grow larger, it makes sense to specialize. Sometimes it's more fun too. Why perform all the policy development if you just love reading hexadecimal TCP dumps all day? There has to be somebody who loves all that "wordy" stuff, right?
Related Content
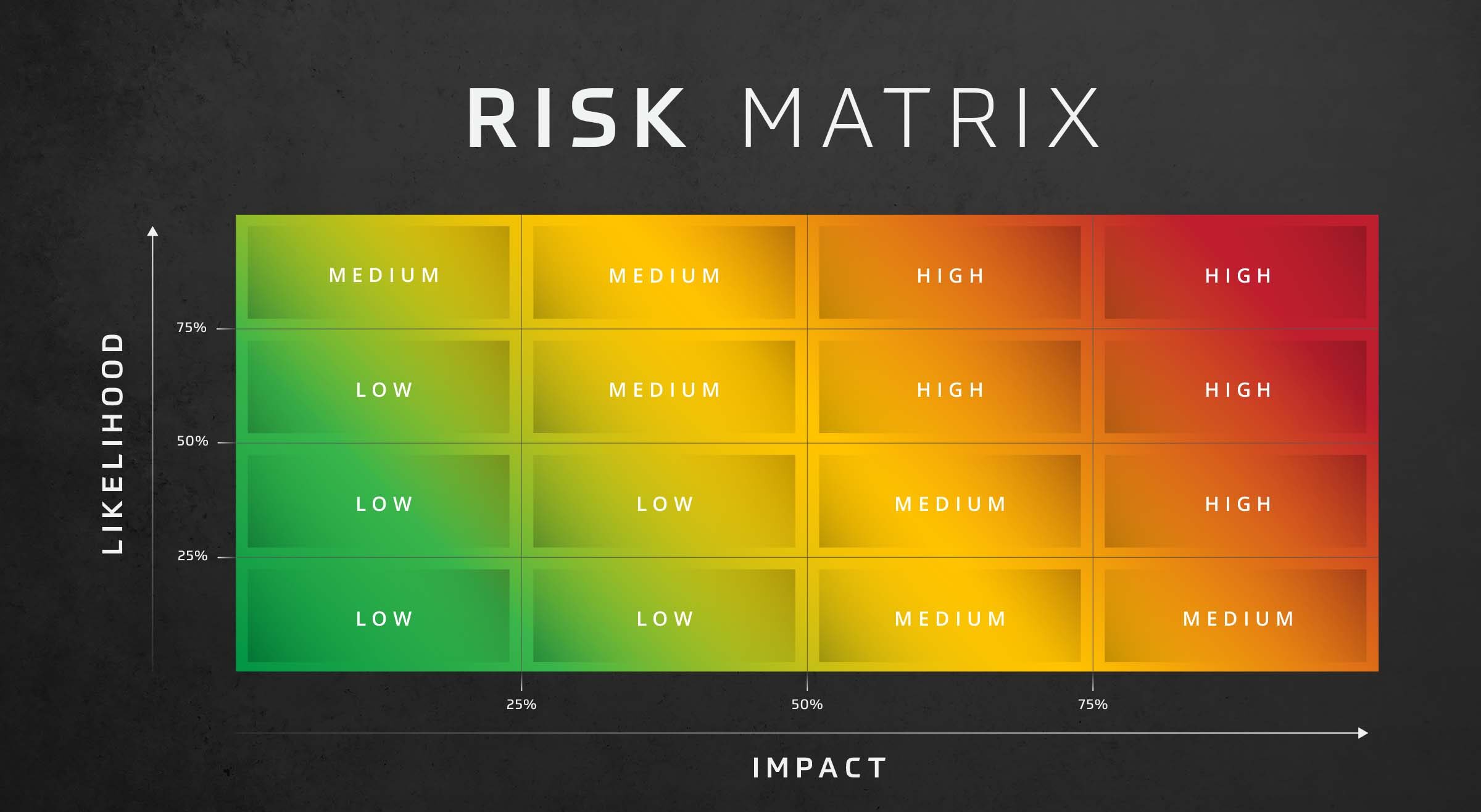
Risk Assessment: Likelihood and Impact
Assess risk effectively with the risk assessment likelihood and impact matrix. This decision-making matrix assesses risk based on the likelihood and impact of threats in your organization.

Cybersecurity Risk Assessment
Optimize your security with an HBS Cybersecurity Risk Assessment. Identify vulnerabilities, manage risks, improve your cybersecurity posture.

IT Company Assessing Risk to Protect Clients
A company managing clients’ IT infrastructure can’t afford a breach. That’s why this IT solution provider took recommendations from their colleagues and hired HBS to conduct a risk assessment.