Security Requirements of Vendors and Clients
- Written by: Jordan Engbers

The following is an excerpt from the paper "Giving Security the Attention It Deserves: An IT Director's Guide to Communicating Security Needs with the Executive Team"
As security awareness rises, so do expectations of vendors and clients. Organizations have begun including information security as a major emphasis in their due diligence process. Vendors and clients are actively searching for partners that value security and make it a top priority.
It is not uncommon for companies to lose out on business due to their lack of security controls. Many organizations won’t do business with a company that hasn’t received SOC 2 Compliance Reporting (service organizations) or gained compliance with HIPAA (healthcare), PCI (payment card), or FISMA (Federal contracts) requirements. Has your company suffered due to a lack of security controls? Security is too important to ignore. Take-charge, and your business will benefit.
Security Professionals Talking Business with Executives
When talking with executives about your company’s security position, be organized. This doesn’t mean that you have to deliver a PowerPoint presentation every time you conduct a meeting, but you should have your security plan in order. You will be expected to answer some pointed questions, and you may only get one shot.
Start with a Conversation
Start by asking some of your own questions. Establish a two-way conversation, and clearly explain the situation. This approach will give insight into the perspectives of the executives. Use this as an opportunity to learn from them and to build your case.
Questions you can ask to get a conversation started:
- How would you describe our brand and what it means to our customers/clients?
- What have we done, and continue to do, to build our reputation?
- What are our plans for our brand in the future?
- Do you have any concerns with our business’ security risks? If so, what are they?
- Has our executive team discussed a strategic security plan?
- Have we lost any prospective business due to a lack of security controls?
The above questions get executives thinking about everything they have done to help build and grow the company. There is much pride in that effort, which you can leverage when communicating the ways that security, or lack thereof, will directly impact their efforts.
Take advantage of the opportunity to meet with executives, and be prepared to support your analysis and recommendations. If you do not already understand the executives’ approach to business, then take some time to learn their perspectives. After all, they will make the decision on whether or not you get the funding you need.
For the complete IT Director's Guide to Communicating Security Needs with Executives, download this paper.
Related Content
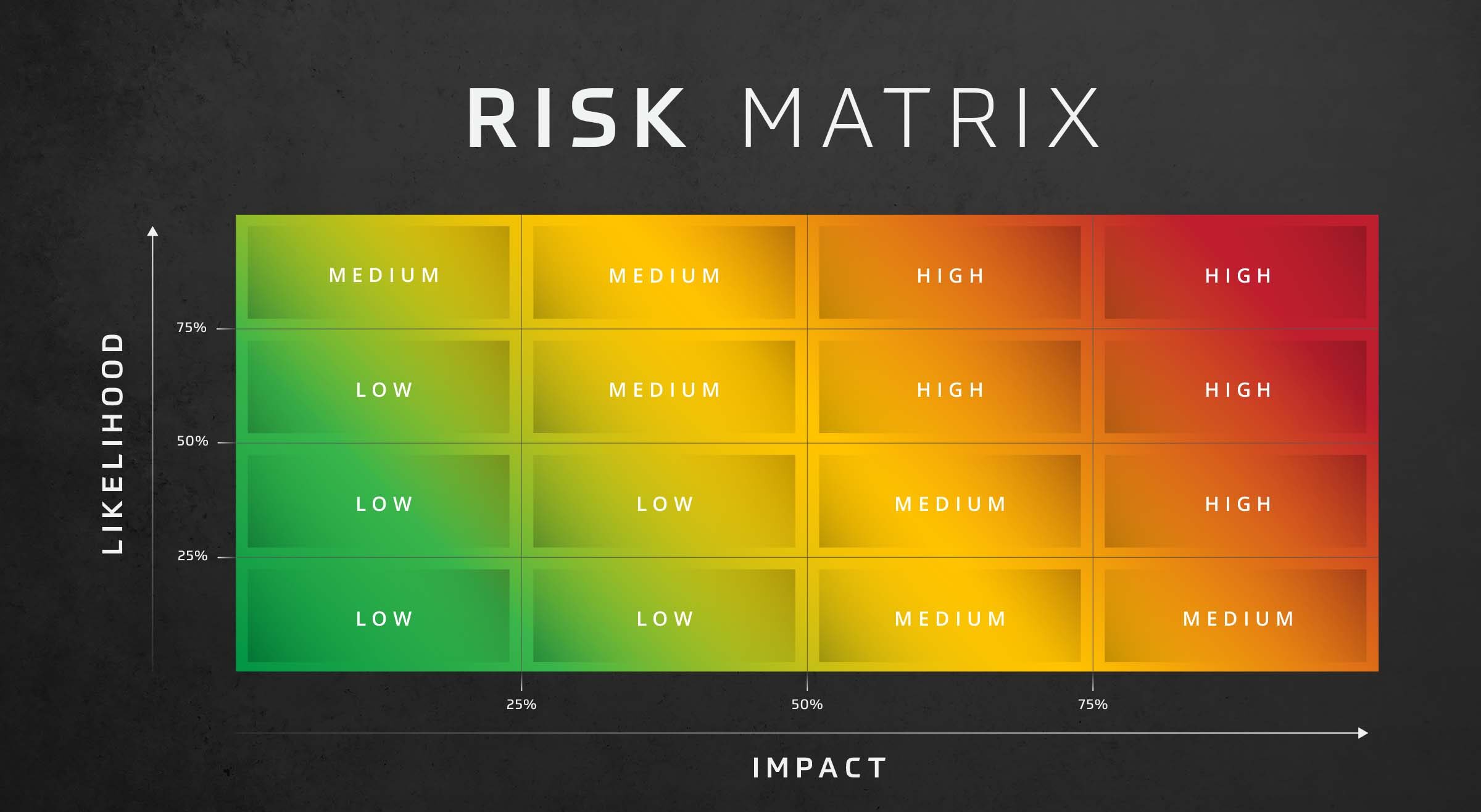
Risk Assessment: Likelihood and Impact
Assess risk effectively with the risk assessment likelihood and impact matrix. This decision-making matrix assesses risk based on the likelihood and impact of threats in your organization.

How Should I Respond to My Clients’ Security Requests?
Vendors are often asked to fill out several security questionnaires by multiple clients. We put together 5 Guidelines for responding to client security risks.

Best Practices for Third-Party Risk Management
Learn how to protect your business with third party risk management (TPRM). Best practices, vendor assessments and frameworks explained.