Work-From-Home Security Lessons Learned
- Written by: Trevor Meers

In the spring of 2020, IT teams had a matter of days to retool their environments to handle entire staffs working from home. Under normal circumstances, that shift would’ve been rolled out meticulously over years. What security lessons have we learned in the two years of this great experiment? In this recap, we check in on lessons learned about the human and cybersecurity implications of scattering data and workers to any location with a solid internet connection.
Security Upgrades Move to the Front
The work-from-home revolution work introduced a host of new data security threats overnight. Employees working remotely log in through unknown WiFi connections, including vulnerable public networks in places like coffee shops. Data moves off corporate servers and into cloud settings. Personal vigilance wanes without the peer pressure of nearby co-workers.
All this gave many IT leaders the motivation (and executive support) to step up security programs during the pandemic. A December 2021 survey from software company MalwareBytes showed that 74% of IT decision makers had implemented new security tools since the spring of 2020, and 71% had implemented new cybersecurity training. As a result, 56% of IT leaders say their environment is slightly or significantly more secure than before the shift to work-from-home. If your security posture looks basically the same as it did in January of 2020, you’re probably leaving a lot of doors open to attackers.
Threats from People You Trust
Even if your team rose to the security challenge, your larger data ecosystem could still pose a problem. Jim Pray, chief technology officer at the Iowa law firm BrownWinick, says many of the cyber attacks his office saw during Covid came in through clients’ systems.
“We saw a big influx of our clients being hit because they weren’t prepared to go to work-from-home. They were getting Office 365 phishing hits, and then the hackers were trying to phish us by using the client accounts,” Pray says.
He’s describing a type of business email compromise scam, a category of cyber crime that exploded over the last two years. In these attacks, hackers take over someone’s email account and pose as a trusted partner. Many of the schemes have fooled workers into sending hundreds of thousands of dollars to fraudulent accounts. And people working from home make easier targets. In the past, an employee may have walked down the hall to confirm a message from a colleague. If that person is working at home, they may just click the link to speed things up.
User Experience Gets Its Due
These attacks illustrate a core fact of cybersecurity: Most cyberattacks start with a social engineering fail, such as an end user opening a malicious email attachment or unknowingly giving their login credentials to a hackers’ site. That means every cybersecurity program rests on enlisting every employee as a frontline defender.
But remote work and the pandemic have heavily eroded users’ cyber wariness. Working off-site can introduce distractions that chip away at anybody’s vigilance over things like fishy-looking emails. Security experts regularly discuss how to overcome the “fear fatigue” that has maxxed out the number of things we can worry about at any given moment.
vCISO Ben Hall urges open conversations about these challenges. “Encourage people to speak to managers about the issues they’re having, whether that’s having trouble accessing things remotely or just feeling like they’re being watched all the time,” Hall says.
Hall points to “shadow IT” as one big issue. Even if you don’t know the term, you know the situation: Numerous security safeguards make your company’s official technology tools a pain to use. So you just put a file on Google Docs and send the link to your co-workers. Hall says companies must face this reality and either make the official tools easier to use or embrace the shadow tools and make them more secure. “If employees are going to keep using Google Drive, consider a business subscription so you can apply some controls around what’s there and how it’s stored,” he says.
“Make it easier while maintaining security,” Hall adds. “Encourage everyone to be vocal and polite to work on the solution together.”
Empowered Users Replace Punished Users
The best security cultures have learned to stop referring to employees as security vulnerabilities (a common IT attitude) and start viewing them as security assets. That’s not just a matter of semantics.
Many employees see phishing tests “as a gotcha,” BrownWinick’s Pray says. That’s understandable, considering that some companies have posted lists of employees who fail the test or threatened to fire anyone who fails three tests.
That’s sending the wrong message, Pray says. “We want them to know that we don’t want them to click the tests. We want them not to click the test.” Instead of taking a punitive attitude toward those who fail the test, identify ways to improve their performance next time. “If a lot of employees fail a phishing test, I have to see that as a failure on my part, not the employees’,” Pray says. “So we’ve ramped up our training.”
Key Best Practices
If you’re looking for simple ways to gauge your IT program’s security maturity, check how you’re handling these basic policies:
- Multifactor authentication – No security move offers a bigger payoff than implementing multifactor authentication (MFA). MFA may seem like a hassle, but it works so well that the market is essentially penalizing those who aren’t using it. For example, Hall says, “If you’re don’t have MFA in place and you’re looking at cyber insurance, you either won’t get it or won’t get an acceptable premium amount.”
- Live human communication – Old-fashioned MFA should remain part of your arsenal. Hackers have proven that they can infiltrate email accounts and pose as an executive or a client asking for a payment that goes to a fraudulent account. Teach your employees that if something seems iffy, they should pick up the phone and confirm with the email’s sender that the message is legit.
- Limited access – Many companies give too many users too much access to the environment. IT teams may be tempted, for example, to give end users administrator rights on their computers to reduce the number of service calls IT gets. But that could let employees install risky software. And if an employee has a lot of network access, a hacker who gets their credentials can go anywhere the real user can. The right approach is least-privileged access, which limits everyone’s access to no more than the files they need to do their jobs.
- Virtual Private Networks – A VPN lets employees securely log into a company network from anywhere. The issue is that with data increasingly residing in cloud settings such as Microsoft OneDrive, employees may not log into the VPN very often. That’s a problem because critical software updates are typically pushed to end users’ machines when they log into the VPN. That means companies should consider requiring everyone to log into the VPN on a regular basis.
Hall encourages leaders to embrace the inevitably of a changing workforce and find ways to handle it successfully. “We have to control it without being controlling,” he says. “It seems like a hybrid model is going to be a popular one. Encourage your staff to do whatever they need to do their work.”
For help identifying your work-from-home risks and opportunities, contact HBS to talk with one of our cybersecurity consultants.
Related Content
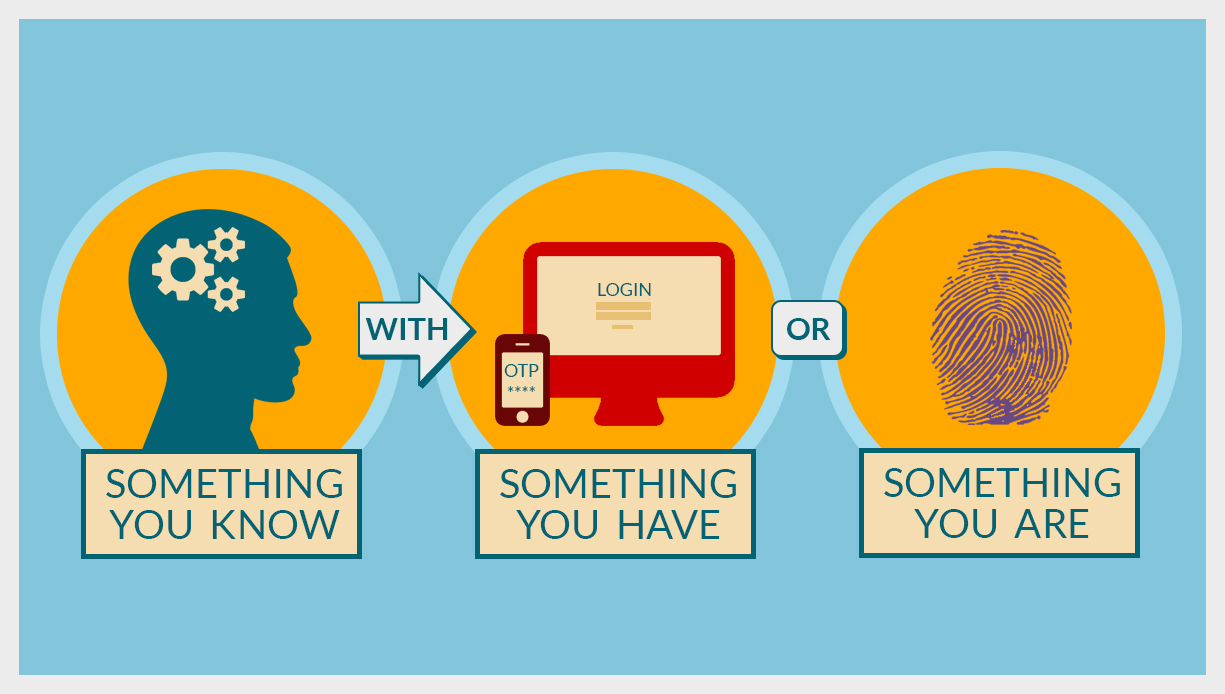
Why is Two-Factor Authentication (2FA) Important for Remote Access?
Remote access systems are under unprecedented attack. Discover how two-factor authentication for remote system administration by IT staff or vendors can help.

The Evolution of Collaboration: The Shift to Hybrid Work
Learn about the shift towards hybrid work and the challenges it brings. This article delves into how HBS’s Collaborate with Webex solution is shaping the future of collaboration.

BYOD Security for Employees: Protecting Both Your Work and Personal Data
8 Key steps for employees to secure personal and work data when practicing BYOD. Learn about strong passwords, software updates, VPNs, data separation, & more.