XDR, MDR and EDR: What’s the Difference?
- Written by: Trevor Meers

If you’re still trying to make sense of XDR, MDR and EDR, you’re not alone. The market doesn't have universal definitions of these terms, and overlap among the solutions makes it easy to drown in the alphabet soup. This blog summarizes the key differences in each solution so you can ensure that you’re using the right tools to secure your environment.
What the “DR” Part Means
The obvious common element in each solution is the DR, which stands for “detection and response.” That means these tools go beyond simply recording an event or blocking software by looking for known malicious signatures. Managed XDR and other DR tools actively assess patterns of malicious activity and shut down suspicious programs, quarantine devices, etc.
DR solutions have proven so effective at reducing attacks that most cyber insurance carriers now require them for anyone seeking to buy or renew a cyber policy. These tools have become a cybersecurity must-have because they address these growing threats:
- Expanded attack surfaces/dispersed workforces – Organizations can no longer lock down all their data on company-owned devices inside the company building. Now you must secure your data in a world where employees are using mobile devices, home networks, etc.
- Hackers lingering in systems – In a typical breach, hackers get into the environment months before administrators realize it. DR detects suspicious activity far sooner.
- Growth in fileless malware – This malware type (also known as non-binary malware) can slip past most antivirus software, which looks for known file signatures. By some estimates, even the best antivirus solutions block only 50-60% of the threats.
EDR – Endpoint Detection and Response
 EDR protects your environment’s biggest vulnerability: endpoints. In the Wild West of remote workforces, employees are using networks you don’t control; sharing devices with family members; installing whatever software they want; etc. In most environments, about 70% of all attacks start with an endpoint.
EDR protects your environment’s biggest vulnerability: endpoints. In the Wild West of remote workforces, employees are using networks you don’t control; sharing devices with family members; installing whatever software they want; etc. In most environments, about 70% of all attacks start with an endpoint.
EDR provides visibility into the endpoints. It constantly logs and monitors activity in order to identify potentially malicious activity on endpoints and take action to stop or mitigate the attack. Rather than looking for file signatures as antivirus solutions do, EDR looks at the behavior of files. With this capability, EDR regularly spots zero-day threats and other attacks that security pros haven’t seen before. In addition to the protection, it looks to provide context around how the attack started and what it attempted to do.
EDR’s powerful response capabilities come from playbooks that guide the solution’s actions after spotting malicious activity. These playbooks determine when to block a file, quarantine a device, etc. Clearly, proper playbook tuning plays an enormous role in not only stopping malicious activity but in preventing a stream of false positives from overly sensitive triggers.
XDR – Extended Detection and Response
Even if you have EDR covering your endpoints, attacks will still arrive through your firewall, cloud workflows, email system, IoT devices, servers and more. XDR provides a holistic view of your extended technology ecosystem, encompassing endpoints as well as every other part, regardless of the vendor that created each component.
XDR’s critical advantage is correlation of events. XDR solutions monitor telemetry data such as Syslogs from across your environment to create a unified response. By leveraging artificial intelligence and machine learning, XDR identifies suspicious patterns amid the millions of system events that occur each day. In simple terms, XDR is designed to notice two seemingly unconnected activities in distant corners of your environment, recognize the pattern of a larger attack and take appropriate action. Without XDR, the left hand may never talk to the right hand, letting attackers lurk in your system far longer before they’re detected.
MDR – Managed Detection and Response
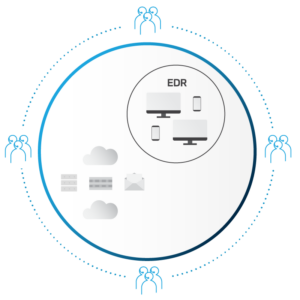
With MDR and Managed XDR, a third party (known as an MSSP or Managed Security Services Provider) manages the tools described above. Management goes far beyond simply responding to alerts. Top MSSPs constantly tune complex XDR solutions in response to emerging threats and your unique environment. Partnering with an MSSP relieves your organization from staffing up to run your own in-house SOC or asking an already-overtaxed IT team to take it on.
A good Managed XDR service has a team of SOC analysts constantly monitoring your environment and tuning the tool for optimal performance. The analysts review alerts and notify you when you should take action. They regularly revise proprietary playbooks and rules in response to an ever-changing landscape. (When the Log4j vulnerability emerged in December 2021, for example, HBS’s SOC wrote new rules for our Managed XDR clients within 12 hours.) In short, a Managed XDR service gives you access to cutting-edge security tools and a team of pros who know how to get the most from the tools.
A Managed XDR service also gives you a big advantage if you face a breach and need support with incident response/digital forensics. Experienced SOC analysts can quickly leverage XDR to develop an attack story that goes far beyond merely stopping the breach. Managed XDR lets you identify all the places the attacker went and what they compromised, ensuring that you can fully stop the breach and recover data more quickly.
To learn more about how Managed XDR service can secure your environment without additional staffing, contact us today.
Related Content

Beyond SIEM: How XDR Maximizes Threat Detection and Response
Discover how XDR overcomes the limitations of traditional security monitoring tools and provides a more robust approach to threat detection and response.

How Managed XDR Makes the Most of the Latest Endpoint Protection Tools
Managed XDR helps endpoint detection reach its full threat-hunting potential as human experts tune the rules for ever-changing situations.

Managed XDR
Enhance security with Managed XDR from HBS: 24x7x365 SOC support, leveraging Microsoft Sentinel & Defender for proactive, adaptive threat defense and response.